3 posts were merged into an existing topic: Обсуждение: неработоспособность ShadowSocks (30.10.2023 +)
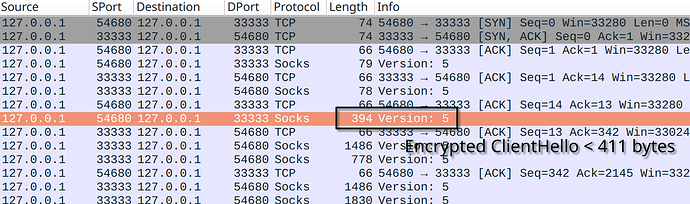
Outline SDK fetch tool produces small TLS ClientHello of 329 bytes, the first encrypted Shadowsocks packet is less than 411 bytes, that’s why you don’t see the block.
$ go run github.com/Jigsaw-Code/outline-sdk/x/examples/fetch@latest -transport 'socks5://127.0.0.1:33333|ss://xxx…' https://ifconfig.co
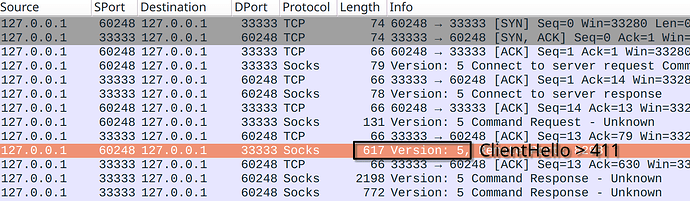
You can use your http2transport + curl to trigger the block.
$ go run github.com/Jigsaw-Code/outline-sdk/x/examples/http2transport@latest -transport 'socks5://127.0.0.1:33333|ss://xxx…' -localAddr 127.0.0.1:44111 &
$ curl -x 127.0.0.1:44111 https://ifconfig.co
curl: (56) Failure when receiving data from the peer
Note that in my tests I was actually fetching HTTP with a padding header to make the first packet larger with -H "Padding: $(printf %800s | tr ' ' 'X')".
I need to check the fetch tool again to make sure the first packet is indeed large. I tested it before with the http2proxy tool and that trick to make the first packet bigger worked after I made a fix to the code (some issue with the HTTP client buffering).
I was actually able to reproduce this same blocking on MTS above. Did you find any inconsistency with my findings?
That doesn’t work, the censor also expects the replies to be of ServerHello/Certificate template based on packet sizes and amount of reply packets.
There should be at least two reply packets for one request packet, and also another request packet.
In other words, the filter expects:
- Client→Server packet with 411+ bytes length (ClientHello)
- Server→Client packet (ServerHello, 100+ bytes of length AFAIK, don’t have notes on hand)
- Another Server→Client packet (Certificate + ServerKeyExchange continuation)
- Client→Server packet (HTTP GET)
Yes — the block is enabled on all cellular operators and all ports.
A post was merged into an existing topic: Обсуждение: неработоспособность ShadowSocks (30.10.2023 +)
So it’s not only the first packet. That is helpful.
I still don’t fully understand the pattern though.
I was able to reproduce the blocking with HTTPS. However, it doesn’t not always happen. DO port 5555 worked on Bee Line and DO port 443 worked on Tele2.
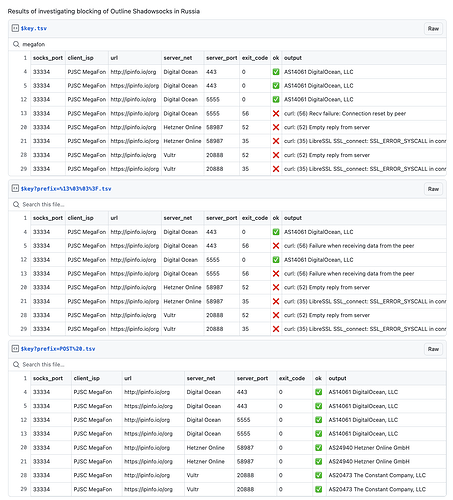
Here are my results:
socks_port client_isp url server_net port exit_code ok output
33333 MTS PJSC http://ipinfo.io/org Digital Ocean 443 28 ❌ curl: (28) Operation timed out after 10002 milliseconds with 0 bytes received
33334 PJSC MegaFon http://ipinfo.io/org Digital Ocean 443 0 ✅ AS14061 DigitalOcean, LLC
33335 Tele2 Russia http://ipinfo.io/org Digital Ocean 443 0 ✅ AS14061 DigitalOcean, LLC
33336 Bee Line Cable http://ipinfo.io/org Digital Ocean 443 0 ✅ AS14061 DigitalOcean, LLC
33333 MTS PJSC http://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33334 PJSC MegaFon http://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33335 Tele2 Russia http://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33336 Bee Line Cable http://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33333 MTS PJSC http://ipinfo.io/org Hetzner Online 58987 0 ✅ AS24940 Hetzner Online GmbH
33334 PJSC MegaFon http://ipinfo.io/org Hetzner Online 58987 52 ❌ curl: (52) Empty reply from server
33335 Tele2 Russia http://ipinfo.io/org Hetzner Online 58987 0 ✅ AS24940 Hetzner Online GmbH
33336 Bee Line Cable http://ipinfo.io/org Hetzner Online 58987 28 ❌ curl: (28) Operation timed out after 10006 milliseconds with 0 bytes received
33333 MTS PJSC http://ipinfo.io/org Vultr 20888 0 ✅ AS20473 The Constant Company, LLC
33334 PJSC MegaFon http://ipinfo.io/org Vultr 20888 52 ❌ curl: (52) Empty reply from server
33335 Tele2 Russia http://ipinfo.io/org Vultr 20888 0 ✅ AS20473 The Constant Company, LLC
33336 Bee Line Cable http://ipinfo.io/org Vultr 20888 0 ✅ AS20473 The Constant Company, LLC
33333 MTS PJSC https://ipinfo.io/org Digital Ocean 443 28 ❌ curl: (28) Connection timed out after 10005 milliseconds
33334 PJSC MegaFon https://ipinfo.io/org Digital Ocean 443 28 ❌ curl: (28) Connection timed out after 10005 milliseconds
33335 Tele2 Russia https://ipinfo.io/org Digital Ocean 443 0 ✅ AS14061 DigitalOcean, LLC
33336 Bee Line Cable https://ipinfo.io/org Digital Ocean 443 56 ❌ curl: (56) Failure when receiving data from the peer
33333 MTS PJSC https://ipinfo.io/org Digital Ocean 5555 56 ❌ curl: (56) Failure when receiving data from the peer
33334 PJSC MegaFon https://ipinfo.io/org Digital Ocean 5555 56 ❌ curl: (56) Recv failure: Connection reset by peer
33335 Tele2 Russia https://ipinfo.io/org Digital Ocean 5555 56 ❌ curl: (56) Failure when receiving data from the peer
33336 Bee Line Cable https://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33333 MTS PJSC https://ipinfo.io/org Hetzner Online 58987 56 ❌ curl: (56) Failure when receiving data from the peer
33334 PJSC MegaFon https://ipinfo.io/org Hetzner Online 58987 35 ❌ curl: (35) LibreSSL SSL_connect: SSL_ERROR_SYSCALL in connection to ipinfo.io:443
33335 Tele2 Russia https://ipinfo.io/org Hetzner Online 58987 56 ❌ curl: (56) Recv failure: Connection reset by peer
33336 Bee Line Cable https://ipinfo.io/org Hetzner Online 58987 28 ❌ curl: (28) Connection timed out after 10003 milliseconds
33333 MTS PJSC https://ipinfo.io/org Vultr 20888 56 ❌ curl: (56) Failure when receiving data from the peer
33334 PJSC MegaFon https://ipinfo.io/org Vultr 20888 35 ❌ curl: (35) LibreSSL SSL_connect: SSL_ERROR_SYSCALL in connection to ipinfo.io:443
33335 Tele2 Russia https://ipinfo.io/org Vultr 20888 56 ❌ curl: (56) Recv failure: Connection reset by peer
33336 Bee Line Cable https://ipinfo.io/org Vultr 20888 56 ❌ curl: (56) Failure when receiving data from the peer
Here is the script
for socks_port in 33333 33334 33335 33336; do
isp="$(curl -s --show-error -p -x 127.0.0.1:1080 --max-time 10 --proxy-header "Transport: socks5://127.0.0.1:$socks_port" https://checker.soax.com/api/ipinfo | jq -r .data.isp)"
for url in http://ipinfo.io/org https://ipinfo.io/org; do
for key in $KEY $KEY5555 $KEY_HETZNER $KEY_VULTR; do
server_net="$(curl -s --show-error -p -x 127.0.0.1:1080 --max-time 10 --proxy-header "Transport: $key" https://checker.soax.com/api/ipinfo | jq -r .data.isp)"
server_port=$(sed -En 's|.*:([0-9]+).*|\1|p'<<< "$key")
output="$(curl -s --show-error -p -x 127.0.0.1:1080 --max-time 10 --proxy-header "Transport: socks5://127.0.0.1:$socks_port|$key" "$url" 2>&1)"
exit_code=$?
if [[ $exit_code == 0 ]]; then
img="✅"
else
img="❌"
fi
echo "$socks_port\t$isp\t$url\t$server_net\t$server_port\t$exit_code\t$img\t$output"
done
done
done | tee table.txt
echo "socks_port\tclient_isp\tserver_net\tserver_port\turl\texit_code\tok\toutput\n$(sort -s -k 3,5 -k 1n -t $'\t' < table.txt)" | column -t -s $'\t'
Note that you can pass the transport to the http2proxy via a HTTP header, so you don’t need to restart it for different transports. I started it with
go run github.com/Jigsaw-Code/outline-sdk/x/examples/http2transport@latest
If I use a simple TCP split on byte 5 (split:5), results are mostly the same, except that a couple more cases are successful with HTTPS (4 vs 2 without the split).
socks_port client_isp url server_net port exit_code ok output
33333 MTS PJSC http://ipinfo.io/org Digital Ocean 443 28 ❌ curl: (28) Operation timed out after 10005 milliseconds with 0 bytes received
33334 PJSC MegaFon http://ipinfo.io/org Digital Ocean 443 0 ✅ AS14061 DigitalOcean, LLC
33335 Tele2 Russia http://ipinfo.io/org Digital Ocean 443 0 ✅ AS14061 DigitalOcean, LLC
33336 Bee Line Cable http://ipinfo.io/org Digital Ocean 443 0 ✅ AS14061 DigitalOcean, LLC
33333 MTS PJSC http://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33334 PJSC MegaFon http://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33335 Tele2 Russia http://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33336 Bee Line Cable http://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33333 MTS PJSC http://ipinfo.io/org Hetzner Online 58987 0 ✅ AS24940 Hetzner Online GmbH
33334 PJSC MegaFon http://ipinfo.io/org Hetzner Online 58987 52 ❌ curl: (52) Empty reply from server
33335 Tele2 Russia http://ipinfo.io/org Hetzner Online 58987 0 ✅ AS24940 Hetzner Online GmbH
33336 Bee Line Cable http://ipinfo.io/org Hetzner Online 58987 28 ❌ curl: (28) Operation timed out after 10005 milliseconds with 0 bytes received
33333 MTS PJSC http://ipinfo.io/org Vultr 20888 0 ✅ AS20473 The Constant Company, LLC
33334 PJSC MegaFon http://ipinfo.io/org Vultr 20888 52 ❌ curl: (52) Empty reply from server
33335 Tele2 Russia http://ipinfo.io/org Vultr 20888 0 ✅ AS20473 The Constant Company, LLC
33336 Bee Line Cable http://ipinfo.io/org Vultr 20888 0 ✅ AS20473 The Constant Company, LLC
33333 MTS PJSC https://ipinfo.io/org Digital Ocean 443 28 ❌ curl: (28) Connection timed out after 10006 milliseconds
33334 PJSC MegaFon https://ipinfo.io/org Digital Ocean 443 56 ❌ curl: (56) Failure when receiving data from the peer
33335 Tele2 Russia https://ipinfo.io/org Digital Ocean 443 0 ✅ AS14061 DigitalOcean, LLC
33336 Bee Line Cable https://ipinfo.io/org Digital Ocean 443 0 ✅ AS14061 DigitalOcean, LLC
33333 MTS PJSC https://ipinfo.io/org Digital Ocean 5555 56 ❌ curl: (56) Failure when receiving data from the peer
33334 PJSC MegaFon https://ipinfo.io/org Digital Ocean 5555 56 ❌ curl: (56) Failure when receiving data from the peer
33335 Tele2 Russia https://ipinfo.io/org Digital Ocean 5555 56 ❌ curl: (56) Failure when receiving data from the peer
33336 Bee Line Cable https://ipinfo.io/org Digital Ocean 5555 56 ❌ curl: (56) Recv failure: Connection reset by peer
33333 MTS PJSC https://ipinfo.io/org Hetzner Online 58987 0 ✅ AS24940 Hetzner Online GmbH
33334 PJSC MegaFon https://ipinfo.io/org Hetzner Online 58987 35 ❌ curl: (35) LibreSSL SSL_connect: SSL_ERROR_SYSCALL in connection to ipinfo.io:443
33335 Tele2 Russia https://ipinfo.io/org Hetzner Online 58987 0 ✅ AS24940 Hetzner Online GmbH
33336 Bee Line Cable https://ipinfo.io/org Hetzner Online 58987 28 ❌ curl: (28) Connection timed out after 10003 milliseconds
33333 MTS PJSC https://ipinfo.io/org Vultr 20888 56 ❌ curl: (56) Failure when receiving data from the peer
33334 PJSC MegaFon https://ipinfo.io/org Vultr 20888 35 ❌ curl: (35) LibreSSL SSL_connect: SSL_ERROR_SYSCALL in connection to ipinfo.io:443
33335 Tele2 Russia https://ipinfo.io/org Vultr 20888 56 ❌ curl: (56) Failure when receiving data from the peer
33336 Bee Line Cable https://ipinfo.io/org Vultr 20888 56 ❌ curl: (56) Recv failure: Connection reset by peer
Prefixes seem to really help.
Using POST%20, almost all connections succeeded. Tele2 was completely successful. Megafon had only one HTTP timeout with DigitalOcean 443. On MTS, HTTP and HTTPS timed out with DigitalOcean 443. On Bee Line HTTP and HTTP timed out on Hetzner.
This reinforces that the blocking is based on random-looking traffic.
Results, sorted by ISP, server network and port:
socks_port client_isp url server_net port exit_code ok output
33333 MTS PJSC http://ipinfo.io/org Digital Ocean 443 28 ❌ curl: (28) Operation timed out after 10006 milliseconds with 0 bytes received
33333 MTS PJSC https://ipinfo.io/org Digital Ocean 443 28 ❌ curl: (28) Connection timed out after 10005 milliseconds
33333 MTS PJSC http://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33333 MTS PJSC https://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33333 MTS PJSC http://ipinfo.io/org Hetzner Online 58987 0 ✅ AS24940 Hetzner Online GmbH
33333 MTS PJSC https://ipinfo.io/org Hetzner Online 58987 0 ✅ AS24940 Hetzner Online GmbH
33333 MTS PJSC http://ipinfo.io/org Vultr 20888 0 ✅ AS20473 The Constant Company, LLC
33333 MTS PJSC https://ipinfo.io/org Vultr 20888 0 ✅ AS20473 The Constant Company, LLC
33334 PJSC MegaFon http://ipinfo.io/org Digital Ocean 443 28 ❌ curl: (28) Operation timed out after 10003 milliseconds with 0 bytes received
33334 PJSC MegaFon https://ipinfo.io/org Digital Ocean 443 0 ✅ AS14061 DigitalOcean, LLC
33334 PJSC MegaFon http://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33334 PJSC MegaFon https://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33334 PJSC MegaFon http://ipinfo.io/org Hetzner Online 58987 0 ✅ AS24940 Hetzner Online GmbH
33334 PJSC MegaFon https://ipinfo.io/org Hetzner Online 58987 0 ✅ AS24940 Hetzner Online GmbH
33334 PJSC MegaFon http://ipinfo.io/org Vultr 20888 0 ✅ AS20473 The Constant Company, LLC
33334 PJSC MegaFon https://ipinfo.io/org Vultr 20888 0 ✅ AS20473 The Constant Company, LLC
33335 Tele2 Russia http://ipinfo.io/org Digital Ocean 443 0 ✅ AS14061 DigitalOcean, LLC
33335 Tele2 Russia https://ipinfo.io/org Digital Ocean 443 0 ✅ AS14061 DigitalOcean, LLC
33335 Tele2 Russia http://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33335 Tele2 Russia https://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33335 Tele2 Russia http://ipinfo.io/org Hetzner Online 58987 0 ✅ AS24940 Hetzner Online GmbH
33335 Tele2 Russia https://ipinfo.io/org Hetzner Online 58987 0 ✅ AS24940 Hetzner Online GmbH
33335 Tele2 Russia http://ipinfo.io/org Vultr 20888 0 ✅ AS20473 The Constant Company, LLC
33335 Tele2 Russia https://ipinfo.io/org Vultr 20888 0 ✅ AS20473 The Constant Company, LLC
33336 Bee Line Cable http://ipinfo.io/org Digital Ocean 443 0 ✅ AS14061 DigitalOcean, LLC
33336 Bee Line Cable https://ipinfo.io/org Digital Ocean 443 0 ✅ AS14061 DigitalOcean, LLC
33336 Bee Line Cable http://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33336 Bee Line Cable https://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33336 Bee Line Cable http://ipinfo.io/org Hetzner Online 58987 28 ❌ curl: (28) Operation timed out after 10003 milliseconds with 0 bytes received
33336 Bee Line Cable https://ipinfo.io/org Hetzner Online 58987 28 ❌ curl: (28) Connection timed out after 10003 milliseconds
33336 Bee Line Cable http://ipinfo.io/org Vultr 20888 0 ✅ AS20473 The Constant Company, LLC
33336 Bee Line Cable https://ipinfo.io/org Vultr 20888 0 ✅ AS20473 The Constant Company, LLC
I got the exact same results when using a TLS prefix that looks like a fragmented record ( %16%03%01%00%C2%A8%01%01).
When using the DNS over TCP prefix (%05%C3%9C_%C3%A0%01%20), the results were worse, but still better than no prefix. It seems it triggered the HTTPS blocking in some cases, but not all cases. This can help figure out the detection rules.
Results:
socks_port client_isp url server_net port exit_code ok output
33333 MTS PJSC http://ipinfo.io/org Digital Ocean 443 28 ❌ curl: (28) Operation timed out after 10005 milliseconds with 0 bytes received
33333 MTS PJSC https://ipinfo.io/org Digital Ocean 443 28 ❌ curl: (28) Connection timed out after 10004 milliseconds
33333 MTS PJSC http://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33333 MTS PJSC https://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33333 MTS PJSC http://ipinfo.io/org Hetzner Online 58987 0 ✅ AS24940 Hetzner Online GmbH
33333 MTS PJSC https://ipinfo.io/org Hetzner Online 58987 56 ❌ curl: (56) Failure when receiving data from the peer
33333 MTS PJSC http://ipinfo.io/org Vultr 20888 0 ✅ AS20473 The Constant Company, LLC
33333 MTS PJSC https://ipinfo.io/org Vultr 20888 0 ✅ AS20473 The Constant Company, LLC
33334 PJSC MegaFon http://ipinfo.io/org Digital Ocean 443 0 ✅ AS14061 DigitalOcean, LLC
33334 PJSC MegaFon https://ipinfo.io/org Digital Ocean 443 56 ❌ curl: (56) Failure when receiving data from the peer
33334 PJSC MegaFon http://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33334 PJSC MegaFon https://ipinfo.io/org Digital Ocean 5555 56 ❌ curl: (56) Recv failure: Connection reset by peer
33334 PJSC MegaFon http://ipinfo.io/org Hetzner Online 58987 52 ❌ curl: (52) Empty reply from server
33334 PJSC MegaFon https://ipinfo.io/org Hetzner Online 58987 35 ❌ curl: (35) LibreSSL SSL_connect: SSL_ERROR_SYSCALL in connection to ipinfo.io:443
33334 PJSC MegaFon http://ipinfo.io/org Vultr 20888 52 ❌ curl: (52) Empty reply from server
33334 PJSC MegaFon https://ipinfo.io/org Vultr 20888 35 ❌ curl: (35) LibreSSL SSL_connect: SSL_ERROR_SYSCALL in connection to ipinfo.io:443
33335 Tele2 Russia http://ipinfo.io/org Digital Ocean 443 0 ✅ AS14061 DigitalOcean, LLC
33335 Tele2 Russia https://ipinfo.io/org Digital Ocean 443 56 ❌ curl: (56) Failure when receiving data from the peer
33335 Tele2 Russia http://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33335 Tele2 Russia https://ipinfo.io/org Digital Ocean 5555 56 ❌ curl: (56) Failure when receiving data from the peer
33335 Tele2 Russia http://ipinfo.io/org Hetzner Online 58987 0 ✅ AS24940 Hetzner Online GmbH
33335 Tele2 Russia https://ipinfo.io/org Hetzner Online 58987 0 ✅ AS24940 Hetzner Online GmbH
33335 Tele2 Russia http://ipinfo.io/org Vultr 20888 0 ✅ AS20473 The Constant Company, LLC
33335 Tele2 Russia https://ipinfo.io/org Vultr 20888 0 ✅ AS20473 The Constant Company, LLC
33336 Bee Line Cable http://ipinfo.io/org Digital Ocean 443 0 ✅ AS14061 DigitalOcean, LLC
33336 Bee Line Cable https://ipinfo.io/org Digital Ocean 443 56 ❌ curl: (56) Failure when receiving data from the peer
33336 Bee Line Cable http://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33336 Bee Line Cable https://ipinfo.io/org Digital Ocean 5555 0 ✅ AS14061 DigitalOcean, LLC
33336 Bee Line Cable http://ipinfo.io/org Hetzner Online 58987 28 ❌ curl: (28) Operation timed out after 10001 milliseconds with 0 bytes received
33336 Bee Line Cable https://ipinfo.io/org Hetzner Online 58987 28 ❌ curl: (28) Connection timed out after 10002 milliseconds
33336 Bee Line Cable http://ipinfo.io/org Vultr 20888 0 ✅ AS20473 The Constant Company, LLC
33336 Bee Line Cable https://ipinfo.io/org Vultr 20888 56 ❌ curl: (56) Failure when receiving data from the peer
I also tried using the POST%20 prefix and it worked. ISP: Tattelecom.
FY, I put the results on the following Gist, which allow you to more easily see all the results and filter by ISP, server network, HTTPS, etc:
had similar symptoms on Tele2 about a month ago, fixed by enabling v2ray plugin
Here is a better dataset with all the measurements in one table:
And here is the decision tree based on that dataset that characterizes the blocking (open in a new tab):
Судя по
блок мешающий работе SS откатили. На T2 так же работает, подтверждаю
И снова включили, поведение аналогичное, с N-го раза ресурсы открываются.
Сегодня днем проявилось на проводном ЭрТелеком, сайты открываются с четвертого-пятого пинка. В telegram текстовые сообщения идут без проблем, но тормозит загрузка медиа.
Перешла на VLESS пока, с ним все хорошо.
На мобильных операторах у меня не проявляется, но теперь проявляется на:
| ISP | AS | Location |
|---|---|---|
| Rostelecom | AS12389 | Orenburg |
| JSC Ufanet | AS60095 | Nizhny Novgorod |
| Rostelecom | AS12389 | Perm region |
A post was merged into an existing topic: Обсуждение: неработоспособность ShadowSocks (30.10.2023 +)
Днем на проводном эртелеком: SS и SS2022, nekoray под windows, hiddify next на дебиане и hiddify next на андроид (через вайфай) - до двух разных серверов на digital ocean (мой и коллеги). На серверах xray, поднятый по инструкции с хабра. Взяла первый попавшийся рабочий носок с 4пда - та же картина, вроде работает, но через три раза на четвертый, так что вроде блок не по хостингу только.
Вечером на проводном Ростелеком: те же клиенты, тот же сервак (уже только мой). SS не пашет, VLESS (xtls-REALITY) нормально.
Регион Нижний Новгород
Да, на мобильных SS на высоких портах продолжал работать все это время
A post was merged into an existing topic: Обсуждение: неработоспособность ShadowSocks (30.10.2023 +)